Pokemon Go Spam Message Campaign
Over the last few weeks Niantic’s location-based augmented reality game Pokémon GO has rapidly become something of a world phenomenon. It is now one of the world’s most popular mobile applications – recently reaching over 100 million downloads. While this explosion in popularity may be good for the developers of the game, it makes fans of the game far more vulnerable to cybercrime. At AdaptiveMobile, we are used to seeing spam that is topical and in line with current affairs. Anytime an issue captures the public’s attention spammers will often try to capitalise on this popularity by sending spam containing content related to that issue. For example, after the recent “Brexit” referendum in Britain we observed lots of “Brexit” spam (which played on the fears of many of the economic effects of Brexit). Similarly, since the release of Pokémon GO we have seen a lot of spam related the app.
Brexit Spam
“Forget Brexit,I WILL MAKE YOU $100,000 IN THE NEXT DAYS!Or I’ll pay you $10,000! [url=http://dyn.co/xxxxx]http://dyn.co/xxxxx[/url] SupportOurCause: [url=http://dyn.co/xxxxx]http://dyn.co/xxxxx[/url] ReplyToStop “
“Look Adison, Here Is a Ridiculously Simple Way That Canadians Can Make 734$/Day After The Brexit! [url=http://xxxx.cash/BrexitDay]http://xxxx.cash/BrexitDay[/url]”
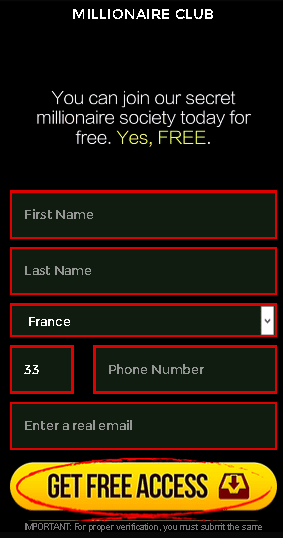

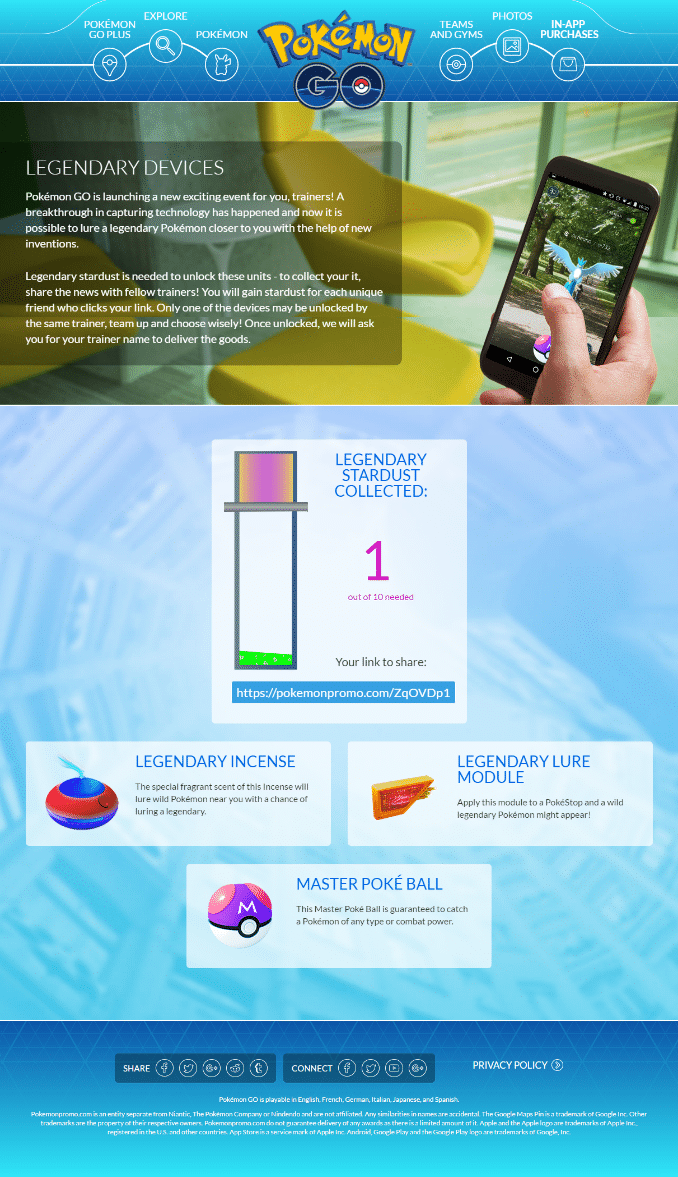
The largest Pokémon GO SMS spam campaign we observed were messages sent to subscribers trying to entice them to visit a website called Pokemonpromo.xxx. Thousands of SMS messages containing a URL to this website were sent to North American subscribers. The website is a sophisticated phishing site that closely mimics the real Pokémon GO site. It claimed to provide the user with additional features to the game if they refer 10 of their friends (likely to spam them as well). This website is no longer active and has been flagged as a phishing site.
Pokemonpromo SMS Message
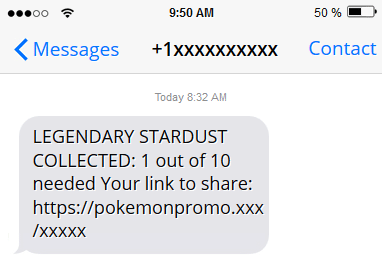
Pokemonpromo Landing Page
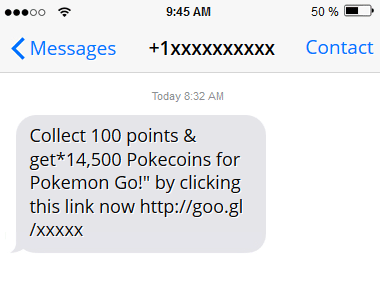
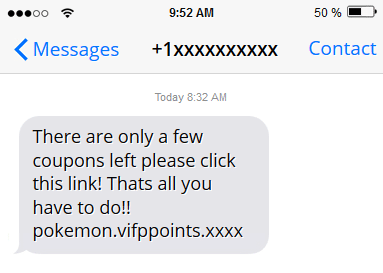
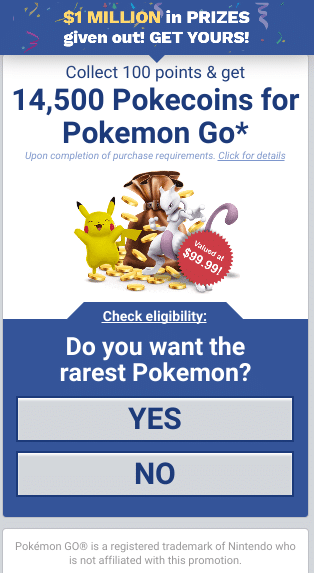
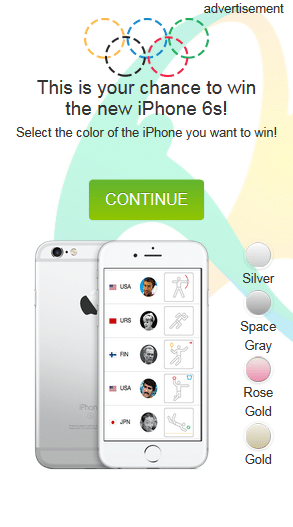
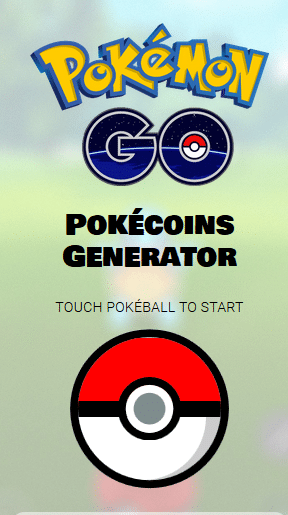
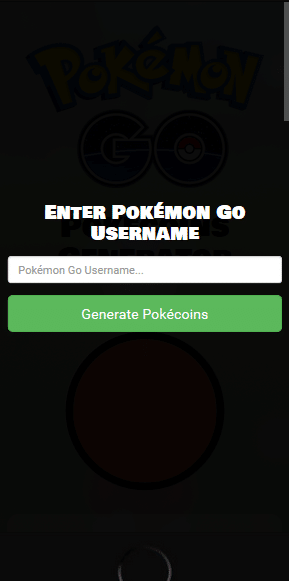
Another Pokémon GO spam campaign offered 14,500 Pokecoins (a type of virtual Pokémon GO currency used for in-app purchases) when you collect 100 points. The messages contained google URL shortened links leading to multiple spam web sites – some of which were Pokemon GO related and others which weren’t. A similar campaign offered a giveaway of Pokecoins on a web site called pokemon.vifppoints.xxxx (and other variations of this URL), where it also prompted visitors to the site to share it with five of their friends. A phishing website called “Pokemon Generator” attempts to lure Pokemon GO users to give their login details so that Pokecoins can be added to their accounts. Links to these sites aren’t only being distributed by SMS – they have appeared on social media sites and Pokémon forums as well.
Pokecoins SMS Spam Messages
Pokecoins SMS Spam Landing Pages
It is likely that we will continue to see Pokémon GO spam for some time – at least until the hype around the app recedes. Until then users of app should apply caution when visiting web sites containing content about Pokémon GO. Be wary of any of any unsolicted SMS messages you receive mentioning the app – particularly if the message contains a URL as this may lead to a phishing web site or a site containing malware.
Thanks also to Mallesham Yamulla for research and contribution to this blog.





