Latest Insight
Enea Retrospective: What Did We Get Right in Our 2023 Trends Report?
Read more
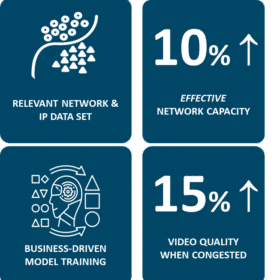
AI & Optimization Boost Capacity Even When Congested
Read moreTags: MNO, Optimization, Traffic Management

Wireless Global Congress Interview: How can Enea help MNOs with Wi-Fi Offloading
Read moreTags: Carrier Wi-Fi, OpenRoaming, Wi-Fi 6, Wi-Fi Offload

